It describes risk assessment of various network security elements. This network security policy template provides policies for protecting confidentiality integrity as well as accessibility of the network.
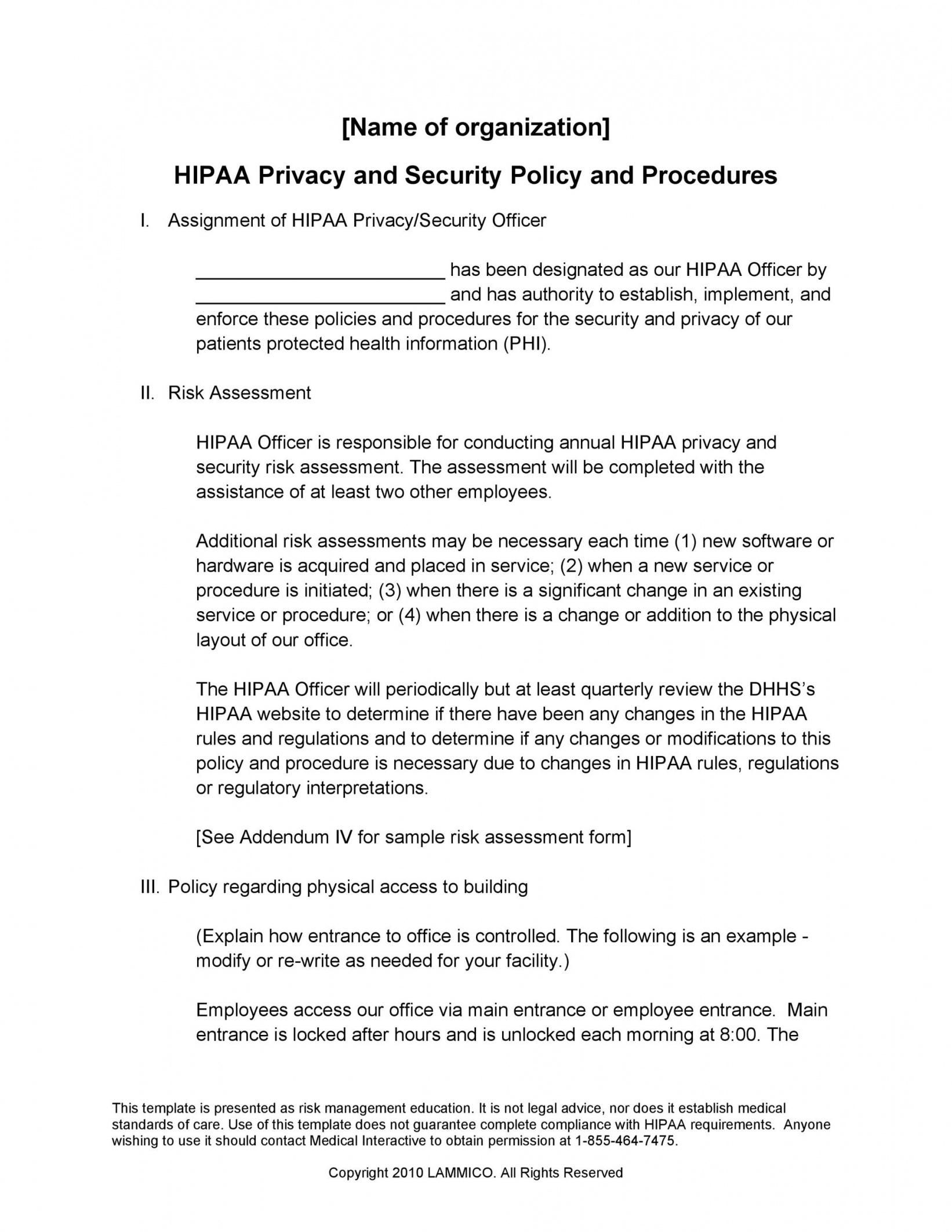
Explore Our Example Of Physical Security Policy Template For Free In 2021 Policy Template Corporate Security Protected Health Information
A policy should also be applied throughout the organization in a consistent manner and provide a reference for.
Network security policy example. Users are responsible for complying with this and all other Texas Wesleyan policies defining computer and network security measures. A network security policy is a set of standardized practices and procedures that outlines rules network access the architecture of the network and security environments as well as. Sample IT Security Policies.
The USF Guest Network is segregated from the internal servers and resources used by authenticated users to keep the network secure. To protect company data and reputation it is essential to ensure that the network is secured. Routers and smart switches provide important security functions within a network.
These include improper sharing and transferring of data. Users of the USF Guest Network are required to provide a valid cell phone number to authenticate. Network Device Security and Configuration Policy.
These issues could come from various factors. Cody Faldyn Purpose The purpose of the policy is to minimize risk associated with Internet and e-mail services and defines controls against the threats of unauthorized access theft of information theft of services and malicious disruption of services. The USF Guest Network is only available in approved areas and require a request to be expanded into any other areas.
SANS has developed a set of information security policy templates. It also institutes security accountability for network security. They spell out what is permitted and what is denied.
No matter what the nature of your company is different security issues may arise. The following articles require Adobe Acrobat Reader. This example security policy is based on materials of Cybernetica AS.
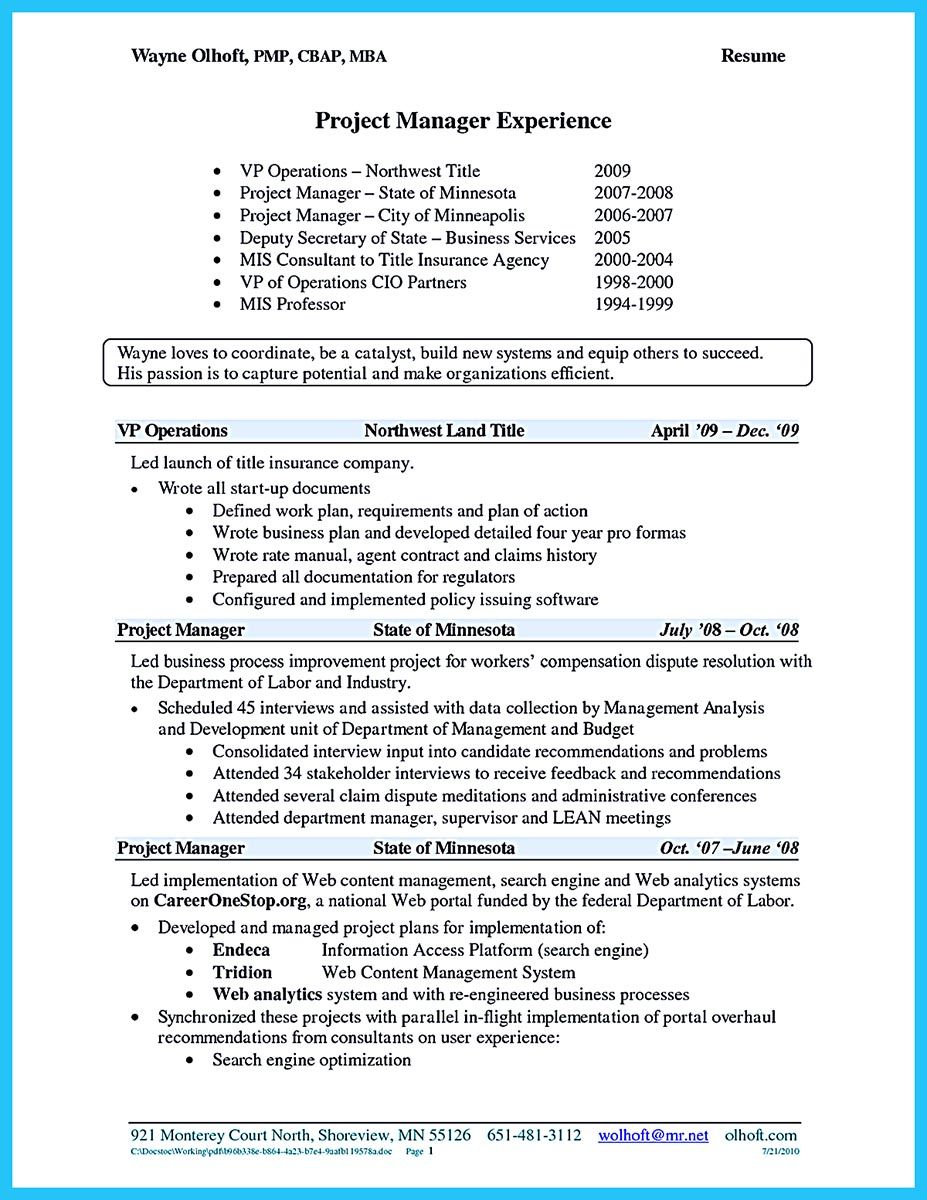
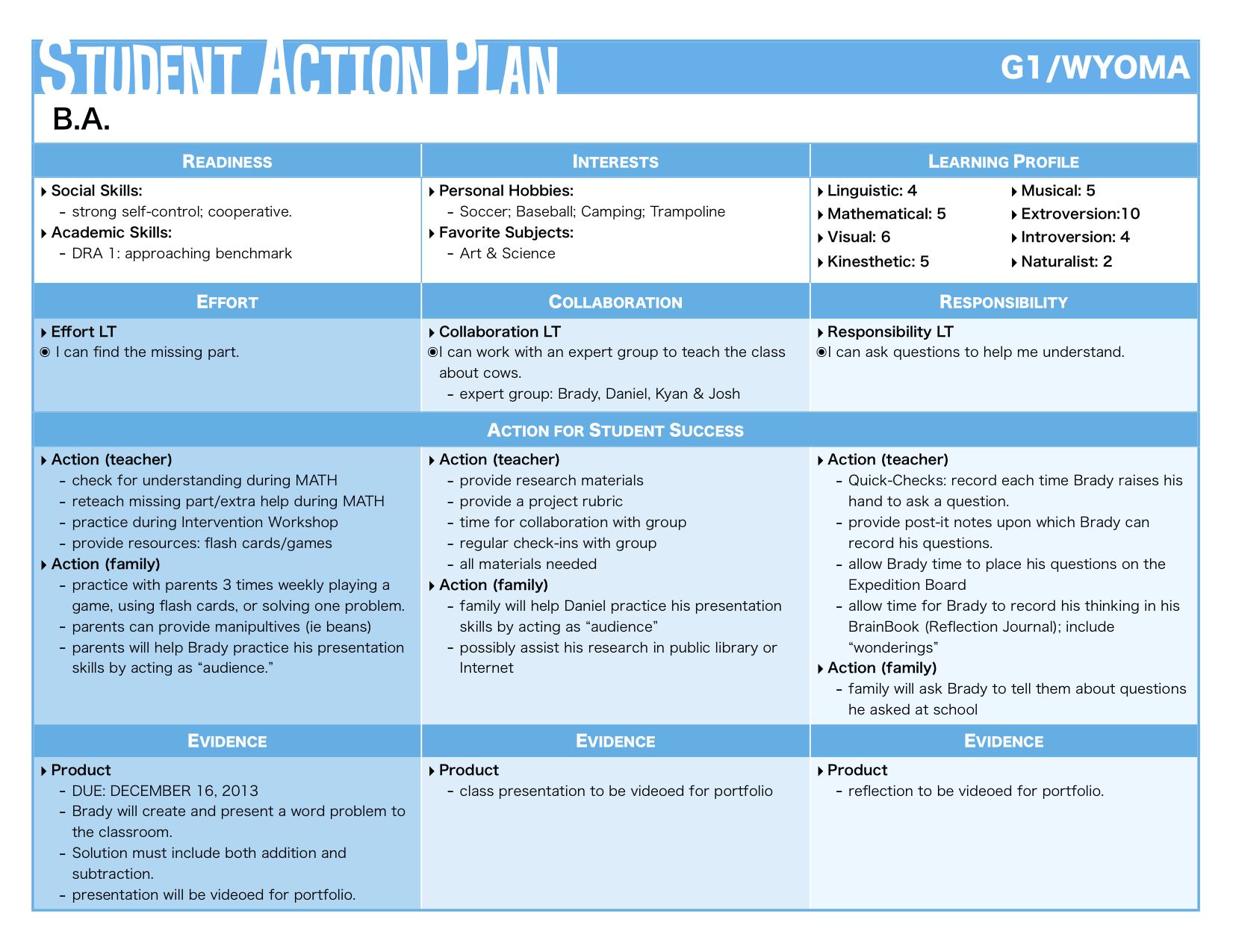
Workstation Full Disk Encryption Using this policy This example policy is intended to act as a guideline for organizations looking to implement or update their full disk encryption control policy. Network Security Policy Created. A security policy enables the protection of information which belongs to the company.
Sample Data Security Policies 5 Data security policy. It can also be from a network security breach property damage and more. Corporate Security Policies Target Audience.
Information Security Policy Templates to Download. If you need additional rights please contact Mari Seeba. Users also are responsible for bringing all known information security vulnerabilities and violations that they notice to the attention of the Information Technology department.
Yellow Chicken Ltd security policy. Virtual Private Network VPN Policy. File servers lab or manufacturing machines systems storing intellectual property.
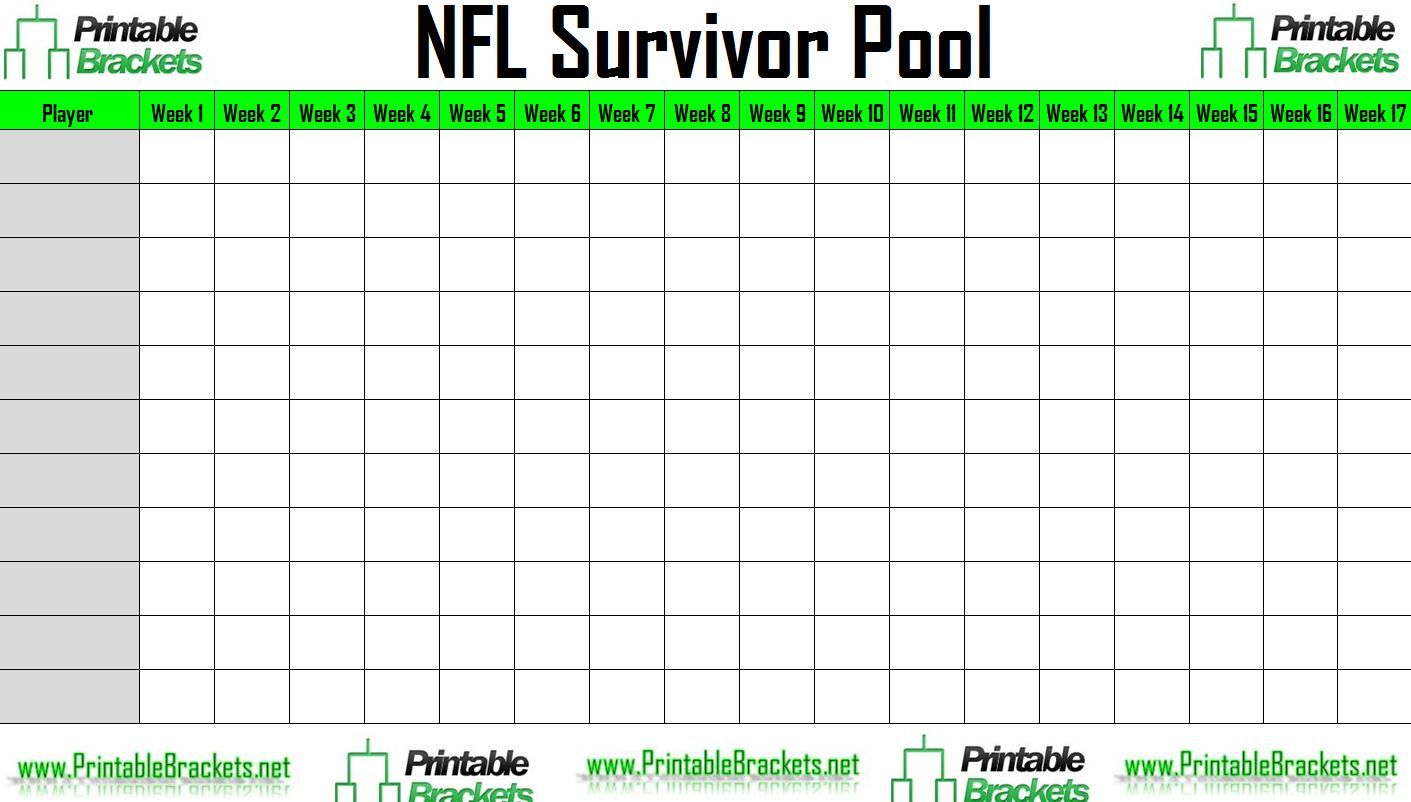
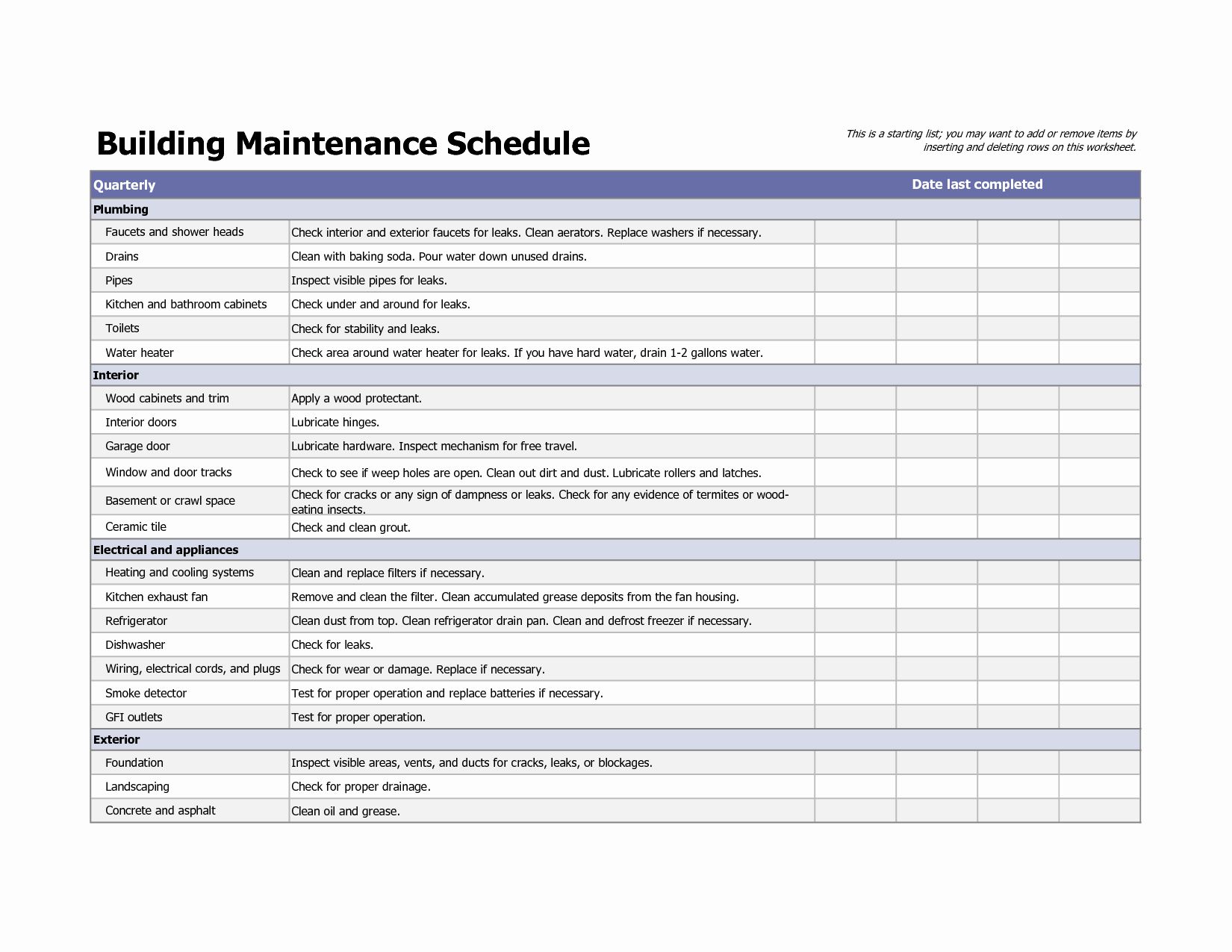
Our list includes policy templates for acceptable use policy data breach response policy password protection policy and more. Youll find a great set of resources posted here already including IT security policy templates for thirteen important security requirements based on our teams recommendations. As all City of Madison network users carefully follow operational and security guidelines we have a good opportunity to continue providing the best.
Each IT policy template includes an example word document which you may download for free and modify for your own use. These are free to use and fully customizable to your companys IT security practices. The latest version of the Network Security Policies and Procedures will always be posted on the City of Madisons EmployeeNet for quick reference.
Network security policy. Each NetworkPolicy may include a list of allowed egress rules. Technical CONFIDENTIAL Page 4 of 14 Network Security Policy Confidential section shall supersede.
Configured correctly they are one of several hardware and software devices available that help manage and protect a. The example policy contains a single rule which matches traffic on a single port from one of three sources the first specified via an ipBlock the second via a namespaceSelector and the third via a podSelector. Sample Network Computer Security Policies.
If you do not already have it you can download it here for free. You are allowed to use it for whatever purposes including generating real security policies provided that the resulting document contains this reference to Cybernetica AS. Free cyber security policy templates to secure your network from ransomware email phishing social engineering attacks and much more.
Computer and network security policies define proper and improper behavior. This can include internal and external systems either company-owned or leasedrentedsubscribed to. Adapt this policy particularly in line with requirements for usability or in accordance with.
Procedures detail the methods to support and enforce the policies and usually describe specific steps to take in regular system. The following are examples of policies weve created. SYSTEM ACCESS CONTROL End-User Passwords.
Physical Security Policy Template. A security policy designates an organizations security controls without specifying technologies as well as offers high-level directives on acceptable and unacceptable actions to protect critical assets. Sample Internet and Email Security Policy GUARDIAN NETWORK SOLUTIONS – DOCUMENT CENTER by.


Information Security Policy Template Luxury 9 It Policy Templates Free Pdf Doc Format Download Policy Template Reference Letter Template Writing A Reference
Information Security Policies Templates Lovely 42 Information Security Policy Templates C Policy Template Job Application Template Certificate Design Template

Cyber Security Proposal Template Business Plan Template Proposal Templates Business Planning